Table Overview on Device and Platform-based Location Requests in the Digital Age
In the wake of modern state-level legislation emphasizing user data protection and privacy, understanding the various ways devices and platforms request location data becomes paramount. The table provided offers a concise overview of how different digital touchpoints — from mobile and desktop devices to web-based applications and smart home devices — handle precise location requests and seek consent.
| Mobile Devices (Android & iOS) |
Desktop Devices (Windows, macOS, Linux) |
Web-based Applications | Smart Speakers and Home Devices | |
|---|---|---|---|---|
| Applications | - System-generated dialog box. - iOS offers "Always," "While Using", etc. - Android offers high/low accuracy location.
|
- System or application-level dialog. - Windows & macOS have location services. - Linux varies by distribution. 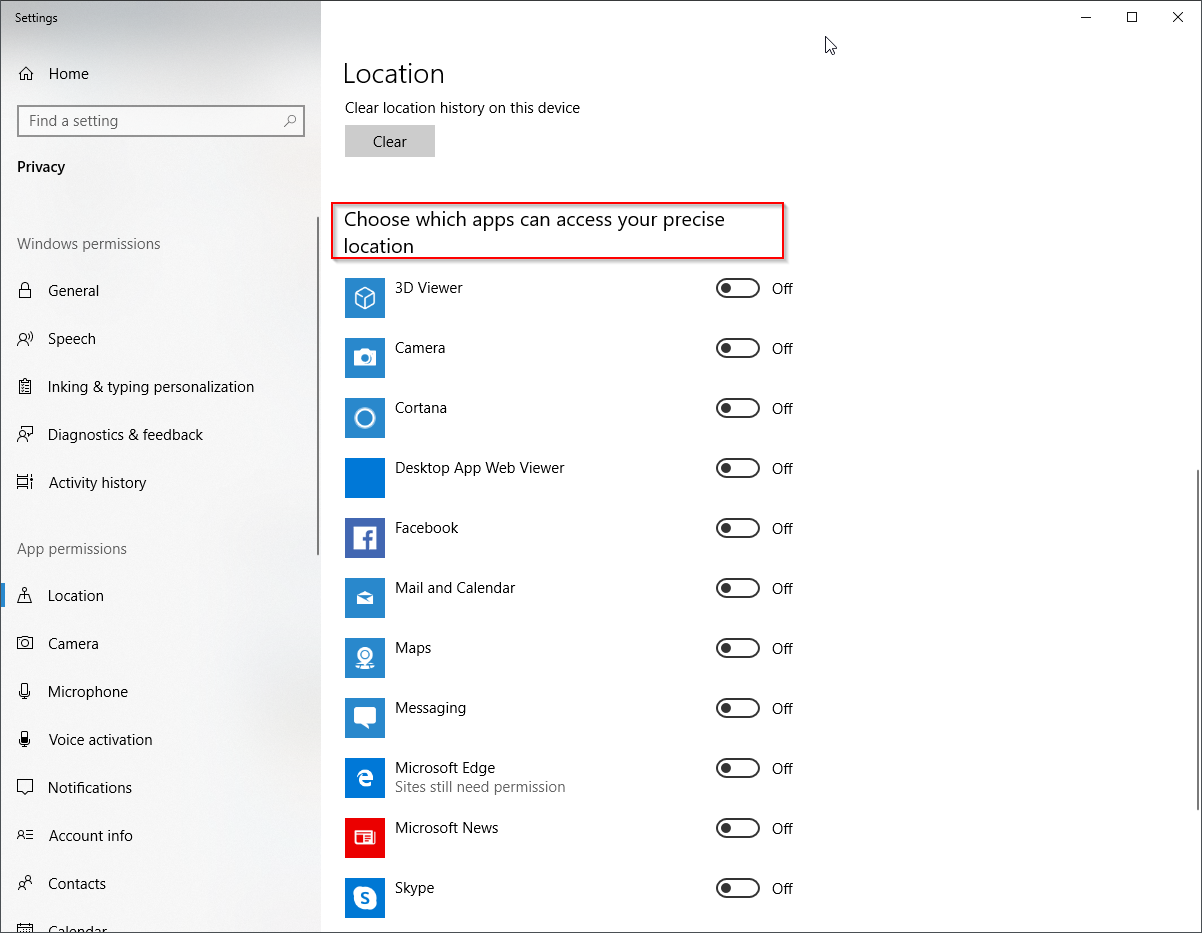 |
- Follows browser's mechanism. | - Via companion mobile app. |
| Browsers | - Browser-generated dialog box. - Options to allow or deny. - Can review in browser settings. 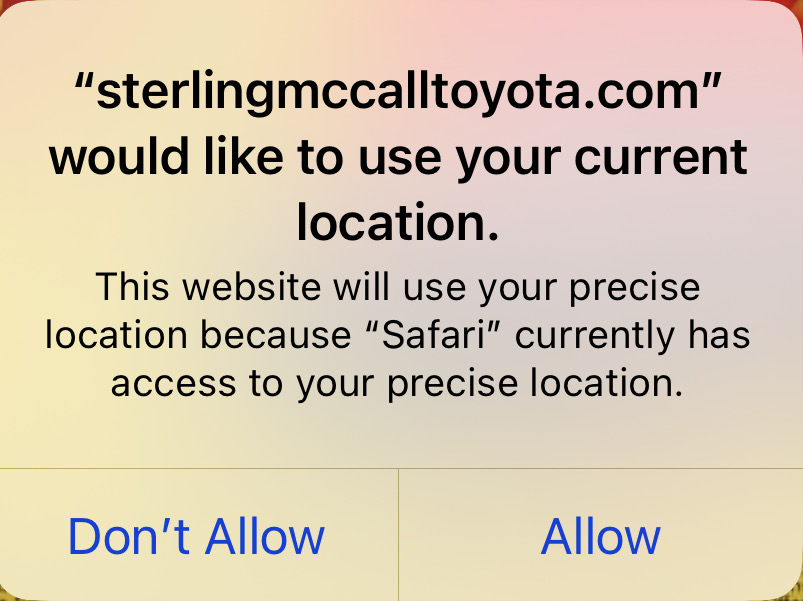 |
- Browser-generated dialog at top of window.
|
- Same as mobile or desktop, depending on access point.
|
N/A |
Consent for location tracking is an essential part of modern device and software design, especially due to growing concerns about user privacy and the implementation of privacy regulations in many regions. Here's an overview of how modern devices like phones, laptops, and browsers seek consent for location tracking:
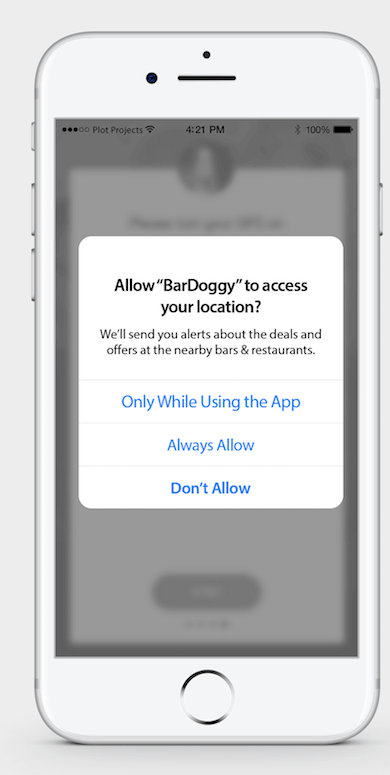
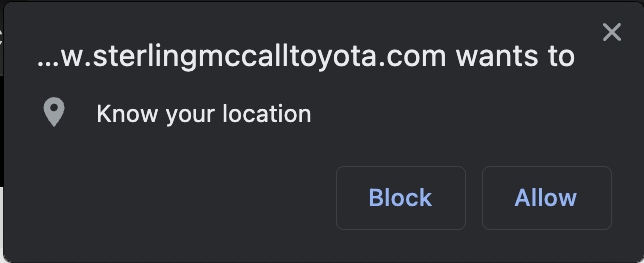
- Explicit Prompt: When an application or website wishes to access the user's location for the first time, it explicitly prompts the user with a dialogue box. The dialogue provides clear information about:
- Which application or website is asking for location access.
- Options to allow or deny the request.
- Granular Permissions: Modern operating systems often provide granular permissions settings, allowing users to:
- Provide location access all the time.
- Provide location access only when the application is in use.
- Deny location access.
- In some cases, select between precise and approximate location.
- Temporary Permissions: Some operating systems and browsers offer a temporary permission option. This means an app or website can access the location just once, and will need to ask again if it requires location in the future.
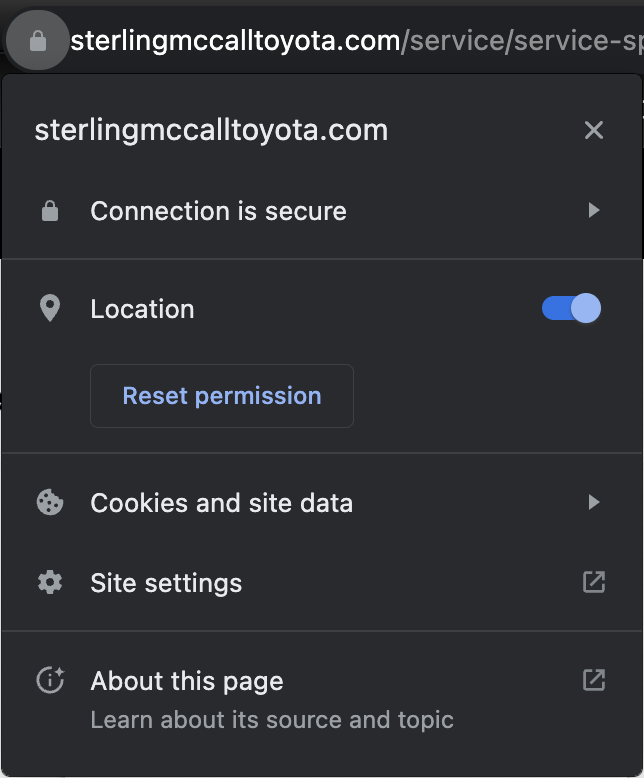
- Settings Menu: Once permissions are given, users can usually change their preferences later from the device or application settings. They can turn off or modify the location access permission.
- Audits and Indicators: On some platforms, there are occasional reminders or indicators showing when an application accesses location. For example, an icon might appear in the status bar. This keeps users informed and reminds them about which apps are using their location.
- Web Browsers: For websites accessed through browsers, the browser itself acts as an intermediary. When a website requests location access, the browser prompts the user, and the user's decision is then communicated back to the website. The user can usually see which sites have location access and can modify or revoke this access through browser settings.
- Compliance with Regional Regulations: In regions with strict data protection laws (e.g., the European Union's General Data Protection Regulation or GDPR), gaining consent for location tracking is not just a best practice but a legal requirement. Violations can lead to significant penalties.
Consent practices are critical not just for user trust, but also for compliance with privacy laws in many jurisdictions. The overarching principle is to ensure that users have a clear understanding of when and why their location data is being accessed, and that they have control over this access.